The single greatest danger to your business isn’t a hacker on the other side of the world, and it’s not your employees taking an extra five minutes on their break. It’s that dusty old server taking up space in a closet, the one that you insist works just fine. Hardware failure and the data loss it leads to can often be enough to set your business back far enough that it can no longer compete, and that’s exactly what we’re here to prevent.
Direct Technology Group Blog
Let’s face it, the Internet is absolutely everywhere, and most likely contributes to your success. That means it is important that your business’ Internet connection meets the requirements of your operations, starting with its bandwidth. Let’s go over what bandwidth actually is, and how to make the most of your Internet service.
Resistance to new technology is a common challenge for businesses. The key to a smooth rollout isn't just about picking the right technology; it's about building a comprehensive strategy that addresses the human element of the change being made. As software is extremely important to any business, having a solid strategy in place to address the governance of your IT systems only makes sense. Today, we’ll give you a baseline on how to build one.
It can be challenging to find reliable IT advice nowadays, particularly when it comes to cybersecurity. Between coworkers with the best intentions and the online influencers selling their guides and platforms, there’s a lot of advice out there. Unfortunately, a lot of it is outdated or incorrect.
This can be actively dangerous where your business’ security is concerned.
Let’s address some of the most common security myths we still encounter far too often.
There has been a good deal of controversy about how personal data has been collected, sold, and used over the past few years. Companies of all types package and sell data to create a valuable extra revenue stream for their business, and while this should be thought of as a side effect of all the data that is created by people, it can also create some pretty difficult situations to try and navigate. Today, we’ll take a look at the data-broker loophole, how it works, and what can be done about it.
Artificial intelligence has become one of the most talked-about technologies throughout every sector of society. It’s being widely used in business, education, and civic life. We want to focus on the latter element and discuss how the U.S. Department of Homeland Security is using AI to improve its ability to keep Americans safe.
Cybercrime is a concern for businesses of all—and we mean all—sizes, from the small mom-and-pop shop down the road to the multinational enterprises, and it’s a concern for a variety of reasons. Let’s take a look at some of the reasons that these massive businesses worry about cyber incidents and see if there isn’t some common ground.
Passwords have been front-and-center for data security since 1960, but even their creator–MIT researcher Fernando Corbató–doesn’t think he should take full credit passwords. In fact, if you brought this up to the researchers who did create them, they would tell you that the security concerns for their time were much more limited.
Privacy for business means a lot more than protecting the data and personal information of clients. It also extends to just about all data collected by a business, including that of the employees. How can you go about protecting this data without also violating the privacy of your employees themselves?
When it comes to your business’ security, your team members can either be your greatest vulnerability or your greatest strength. In order to ensure that the latter is the case, you need to make sure that they are all trained up in the proper security measures. For your convenience, we wanted to share a few tips to help make this training more effective.
Artificial intelligence has taken the world by storm, and with recent improvements to automated technology and machine learning, it should be clear that this technology is not going anywhere anytime soon. With proper implementation, artificial intelligence can help your business cut costs, improve operations, and mitigate unnecessary or repetitive tasks, all of which compounds to create a smoother and more manageable workload for your employees.
Have you ever listened to someone talk about something that they really have a good handle on? One of two things will happen. First, their language will be filled to bursting with buzzwords and jargon that—while they clearly know what it all means—is confusing for a layperson. We can be guilty of this ourselves, so we wanted to take a few moments to take the second option and discuss what they mean in more common terms… and, despite how others may use them, what they don’t.
The 2020 election is months away and traces of it can be seen everywhere. As people quarrel about how social media is being used to interfere with the political process, there is pressure mounting on election officials and tech companies, alike, to do what they can to keep solicitation and corruption out of the ballot box. Let’s take a neutral view of the changes that some online platforms are making to the way that political information is shared.
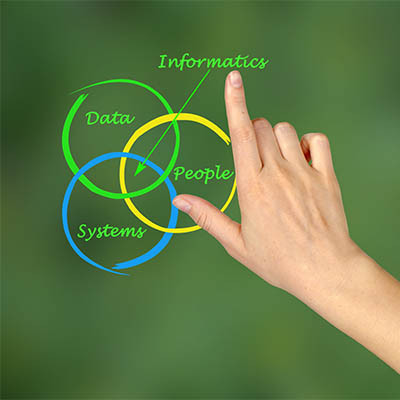
Big data, or massive data sets that can be used to make inferences and reveal patterns, has become an increasingly important part of modern business and can be leveraged in many different ways. There are a few different options for storing this data available, which the use case for the data will dictate. Here, we’ll evaluate whether a “data lake” or a “data warehouse” would better suit your needs.
Huawei has found itself in an... interesting spot lately. Despite being the top telecom supplier in the world and second in phone manufacturing, many countries have banned the use of the Chinese company’s networking equipment. This is primarily due to the close ties Huawei has with China’s government, and the potential spying Huawei could do.