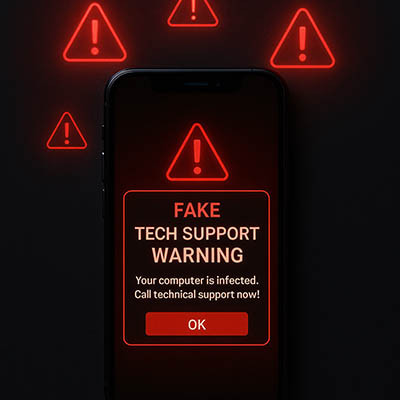
The bigger your business’ workforce, the bigger your overall digital footprint… and the bigger a task it becomes to properly manage who has access to what. Make no mistake, this task is a critical one to complete for the sake of your security and, ultimately, your reputation and success.
Let’s go over how this situation arises and discuss how to avoid it through identity governance.